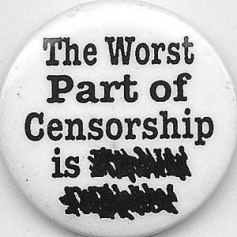
 On the 3rd March the Libyan government took the unprecedented step of making the internet indefinitely unavailable for all but a few within its borders using ‘kill switch’ censorship tactics. Whilst ‘kill switch’ censorship has been used before (and since, in Syria July 3rd), in Nepal 2005, Burma 2007 and Egypt earlier this year, what is unique about the situation in Libya is the duration of which the internet has been stifled. The implications of this kind of action are many: 1/ The information available to the wider community becomes limited to that which is produced by state controlled media; 2/It acts to disable the spread of information that upholds opposition ideologies and paradigm shifts; 3/It acts to disable international lobby potential. The internet can and has been used to raise international awareness of human rights violations and opposition political groups and to mobilise international pressure against offending governments. More recently popular social networking sites such as Facebook and Twitter have been used to widen the reach. Governments tend to exercise more behavioural restraint when being judged by the international community at large and other more powerful entities like the UN and US government. Cutting the internet cuts some of the exposure from opposition voices within the offending country (Chowdry, 2008); and 4/ Being connected to information is vital for lifelines of the revolution, those with important roles in the crisis (doctors & medical staff, aid agency teams and active rebels) must seek alternative and perhaps less efficient ways of communicating.
On the 3rd March the Libyan government took the unprecedented step of making the internet indefinitely unavailable for all but a few within its borders using ‘kill switch’ censorship tactics. Whilst ‘kill switch’ censorship has been used before (and since, in Syria July 3rd), in Nepal 2005, Burma 2007 and Egypt earlier this year, what is unique about the situation in Libya is the duration of which the internet has been stifled. The implications of this kind of action are many: 1/ The information available to the wider community becomes limited to that which is produced by state controlled media; 2/It acts to disable the spread of information that upholds opposition ideologies and paradigm shifts; 3/It acts to disable international lobby potential. The internet can and has been used to raise international awareness of human rights violations and opposition political groups and to mobilise international pressure against offending governments. More recently popular social networking sites such as Facebook and Twitter have been used to widen the reach. Governments tend to exercise more behavioural restraint when being judged by the international community at large and other more powerful entities like the UN and US government. Cutting the internet cuts some of the exposure from opposition voices within the offending country (Chowdry, 2008); and 4/ Being connected to information is vital for lifelines of the revolution, those with important roles in the crisis (doctors & medical staff, aid agency teams and active rebels) must seek alternative and perhaps less efficient ways of communicating.
Circumvention methods for ‘first-generation’ censorship practices, such as firewalling are fairly extensive and straightforward. The Citizen Lab of the University of Toronto has put together a user friendly guide to bypassing 1st – gen censorship; Everyone’s guide to by-passing internet censorship (2007), which is available in several languages, although I am still awaiting a response from the Citizen’s Lab as to whether the guide is available in Arabic. If and when a copy becomes available I will post the link on the links section. It’s a very succinct easily digestible guide on how to circumvent censorship using simple already available/downloadable tunnelling software. The guide outlines the risks and benefits of using public vs private computers for circumvention and the role of ‘outsiders’ in circumvention support. It discusses in some detail currently available circumvention software.
From my own research, other software includes but is not limited to hidemyass, hotspot, yourfreedom and disposable email addresses (often included within the circumvention software) including hushmail, spamex, spamgourmet, E4ward, Gishpuppy, Mailnator and Yahoo! Mail Classic (keeping in mind that in 2003 Yahoo! helped the Chinese government to expose and incarcerate Li Zhi, for his role in online message board criticisms of the regime, by handing over details of his email account to the authorities). For net activists, the Citizen’s Lab have also produced a guide for anonymously publishing online. There are as many techniques for circumventing as there are for censoring. Censorship and circumvention is a perpetual cycle; bypassing ‘kill switch’ censorship is the new challenge for hackers of the future.
The current circumvention techniques for bypassing ‘kill switch’ service attacks, such as the blackholing of IP addresses that has happened in Libya, are slightly more old school and much more limited; I’ve put together a small list of ideas which I have compiled from various online sources. The easiest way to access the internet when connectivity has been damaged centrally is to use dial-up internet. PC World have written a great article on what you need to get connected. Whilst it may sound simple, having the right equipment and software is essential to make the connection and this may require advanced planning and preparation.
Internet Relay Chat is a kind of internet text messaging done in real-time. This kind of messaging can be sent to groups or privately to individuals, but it requires both software and a dial up server – both would already need to be in place to make it possible. As an alternative, Point-to-Point (serverless) chat is available through Microsoft NetMeeting, ACHAT, and others. “ This allows a direct communication between any two computers that can ‘see’ each other on the network. The network in this case could definitely consist of one computer calling another directly, over the phone lines” (Ketcham, 2011).
Other, more prevalent, forms of technology are currently being used through internet blackouts and where the internet is not commonly used; Mobile phones, whilst also being subject to disrupted services & monitoring, are the most obvious and widespread means of communicating and ham-radio has recently been employed as an alternative.
More modern technologies for circumventing this type of censorship do not currently exist and according to Richard Stiennon of IT-Harvest, overcoming this type of censorship would involve Freedom Fighters building “clandestine Internet infrastructure including satellite links and cables strung across borders,” which is precisely what is happening now in Benghazi, as we begin to see new independent media emerging. WirelessU is an organisation working towards training individuals how to set up their own wireless communications. They have produced a guide to wireless networking, Wireless Networking in the Developing World: A Practical Guide to Building Low-Cost Telecommunications Infrastructure. This is a comprehensive and detailed 425p manual on wireless networking which is not for the faint-hearted. The book supports people to build high speed data networks using locally available resources: “Using inexpensive off-the-shelf equipment, you can build high speed data networks that connect remote areas together, provide broadband network access in areas that even dialup does not exist, and ultimately connect you and your neighbors to the global Internet” (2007).
Satellite communications already play a significant role in crisis. Humanitarian organisations working in crisis situations depend on satellite technology & the organisations who are responsible for setting up the technology like the UN-ITU, Telecoms sans Frontieres and Humaninet. Satellite services & kits are also being sold to individuals for their personal needs. For most people living in Libya satellite coms would be the more pricey option, but for organisations and businesses, who have a communications budget, satellite is a straightforward and effective option.
For Distributed Denial of Service Attacks (DDoS) there are no circumvention techniques, rather an organisation must tactically prepare and make provisions for the event. The Berkman Center for Internet & Society at Harvard University, discuss methods for mitigation in their article on The Distributed Denial of Service Attacks Against Independent Media and Human Rights Sites:
-Application attacks can be strongly mitigated by replacing complex content management systems (CMSes) with static HTML or by adding aggressive caching systems to deliver content at the expense of interactivity.
– All organizations should carefully consider whether to host their sites on a free, highly DDoS resistant hosting service like Blogger, even at the cost of prestige, functionality and possible intermediary censorship. Organizations that choose to host their own sites should plan for attacks in advance, even if those plans include acceptable levels of downtime.
– Organizations that choose to host their own sites should use systems to detect attacks and, when necessary, degrade site performance and retreat to backup hosting on a free, highly DDoS-resistant hosting service like Blogger. Simple modules for popular content management systems could automate this process and minimize the disruption of an attack.
– Human rights funders should identify and support local experts in communities of the attack sites, since defending against DDoS and other attacks requires not only technical skill but also knowledge about and trust of each of the local communities.
– Human rights funders should consider funding a coordinator to identify both local experts for human rights communities and core network organizations willing to help human rights sites and to help local experts and core networks organizations work with one another.
– The human rights community should work with Internet service providers (ISPs) and online service providers (OSPs) to identify providers who will work to protect sites from DDoS and who will agree not to remove controversial content unless required by law.
– We propose a broad public discussion of a range of policy responses to the rise of DDOS attacks against independent media organizations and human rights groups, with a view toward a sustainable long-term approach that balances the range of legitimate interests involved.
(E. Zuckerman, et al, December 2010)
Preparation is the key to communicating through Service Attacks. Stiennon recommends Threat Based Management approach. He says: “Threat Based Management (TBM) is an alternative to risk based management (RBM). In RBM you identify critical assets first, then determine how much to invest to protect them. This is actually hard to do as every ICT asset is considered critical by someone. TBM starts by evaluating the threat and taking measures to thwart the threat before it becomes overpowering. Phishing, spyware, and cyber crime are three examples of threats. State sponsored cyber espionage is the current threat that organisations should be countering. Government “kill switches” are a threat to freedom of information and communication during crisis. Unfortunately there are rarely official organisations in place to consider this threat before the crisis appears.” Like the Berkman Center, Stiennon suggests a need for collaborative organisation to address the issue of ‘preparedness’ in communicating through crisis.
What would you put in your internet crisis kit? To submit ideas communicationcrisis@live.co.uk
For more information on this topic:
Humaninet – http://www.humaninet.org/prepare.html
IT Harvest – http://www.it-harvest.com/CDW
Infowar Monitor – http://www.infowar-monitor.net/
The Citizen Lab – http://citizenlab.org/
Arbor Networks’ Infrastructure Security Reports – http://www.arbornetworks.com/report
For further reading on this topic:
Distributed Denial of Service Attacks Against Independent Media and Human Rights Sites, Ethan Zuckerman, Hal Roberts, Ryan McGrady, Jillian York, John Palfrey, The Berkman Center for Internet & Society at Harvard University
December 2010
Everyone’s Guide to Bypassing Internet Censorship: For Citizens Worldwide, The Citizen Lab, 2007.
Wireless Networking in the Developing World: A practical guide to planning and building low-cost telecommunications infrastructure, Flickenger et al, 2007.
Access Controlled: The Shaping of Power, Rights, and Rule in Cyberspace, Ronald J. Deibert, John G. Palfrey, Rafal Rohozinski and Jonathan Zittrain eds, 2010.
The Role of the Internet in Burma’s Saffron Revolution, Mridul Chowdhury, 2008
How to Beat a Web Censor, But How Censors Could Still Shut Down a Site, Sanjana Hattotuwa, 2011
Interesting post as always!
I would have thought that mobile phones would provide a bigger possible workaround than you give credit, as mobile ownership is fairly widespread in these parts and would circumvent ‘kill switch’ censorship.
Also did OBL send memory sticks all over the place to evade detection? Couldn’t Libyans and others send physical artefacts to their respective diasporas for uncensored dissemination?
The role of mobile phones is so significant that I intend to dedicate an entire article to the topic. Stay tuned!!
Really interesting point about memory sticks through the post and I hadn’t even considered it. The Libyan postal service is also owned, monitored and run by the Gaddafi regime, but perhaps a clandestine group could do border runs to pass the physical ‘artefacts’ on to safer countries for posting. It might be that something like this is already happening in the liberated parts such as Benghazi. It’s one to look at.
[…] Let’s make some noise: Bypassing internet censorship (via Communication Crisis) Posted on July 11, 2011 by firstpraxis On the 3rd March the Libyan government took the unprecedented step of making the internet indefinitely unavailable for all but a few within its borders using 'kill switch' censorship tactics. Whilst ‘kill switch’ censorship has been used before (and since, in Syria July 3rd), in Nepal 2005, Burma 2007 and Egypt earlier this year, what is unique about the situation in Libya is the duration of which the internet has been stifled. The implications … Read More […]